Introduction
Cyber security risk assessment helps businesses identify threats and apply mitigation strategies to protect data, systems and organisational resilience. Cyber risk assessment has become a critical priority for modern businesses due to the increasing complexity and frequency of cyber threats. Organisations rely heavily on digital infrastructure to store data, manage operations, and communicate with stakeholders, making them vulnerable to cyber attacks.
Cyber Security Risk Assessment in Business Environments
Cyber security risk is a possible loss or damage caused by failures or breaches of information systems. Threats, vulnerabilities and impacts are often viewed as the combination of risk. The threats are related to malicious actors or events, vulnerabilities are system or process weaknesses, and impacts are related to the impact on the organisation.
To businesses, they can include loss of money, legal liability, fines by the regulating authorities, and loss of trust among stakeholders. The systematic cyber security evaluation will allow organisations to understand their critical assets, assess their exposure to threats and priorise their investments towards security. An unstructured evaluation may make businesses have scattered or reactionary security policies, which do not respond to risk drivers.
Cyber Security Risk Assessment Process for Businesses
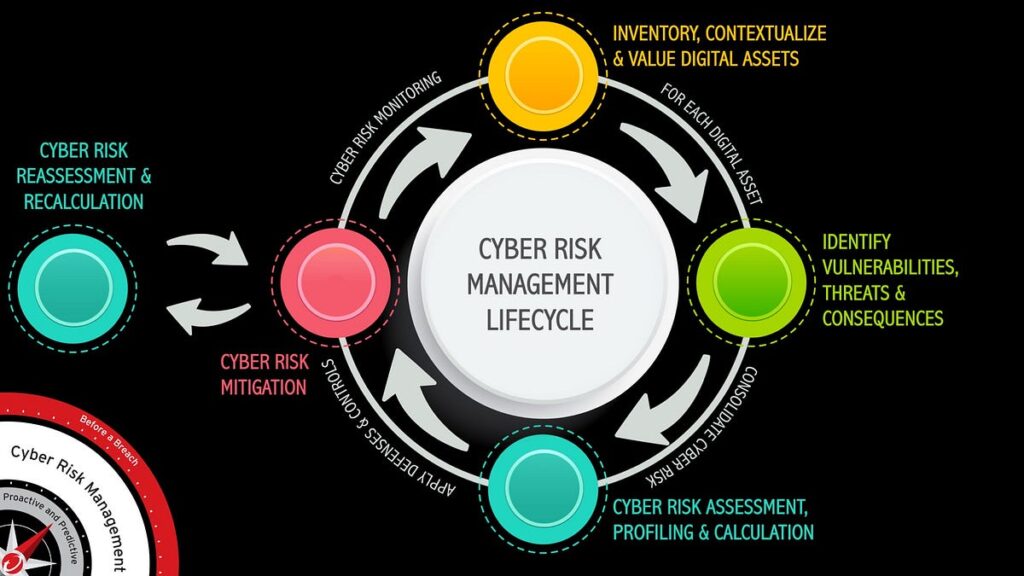
An effective risk evaluation procedure is usually surrounded by a set of organized steps. To begin with, the organisations identify information assets that include financial systems, customer databases, and intellectual property. Second, they study the possible risks, such as external attacks, insider abuse and unintentional system failures. Third, vulnerabilities are evaluated, including use of outdated software, poor authentication tiers or insufficient employee training.
Lastly, calculation of risks is done by approximating the probability and effects of the possible accidents. A lot of companies use established models to go through this process. The ISO 27001, NIST Cybersecurity Framework, and COBIT are among the standards that offer systematic guidelines to know and deal with security risks in cyber security. These frameworks improve consistency, promotion of regulatory compliance, and communication between technical and managerial stakeholders.
Click on the below to read more:
https://wpbk.crea8ive.solutions/wp-admin/post.php?post=27515&action=edit
Common Cyber Security Risks Faced by Businesses
Businesses across sectors face a range of cyber security risks that vary in scale and complexity. The table below summarises common risks and their potential impacts.
Table 1: Common Cyber Security Risks and Business Impacts
| Cyber Security Risk | Description | Potential Business Impact |
| Phishing attacks | Deceptive emails targeting employees | Data breaches, credential theft |
| Ransomware | Malware encrypting systems for financial extortion | Operational disruption, financial loss |
| Insider threats | Malicious or negligent employee actions | Data leakage, compliance violations |
| Unpatched software | Outdated systems with known vulnerabilities | System compromise, service downtime |
| Third party risks | Security weaknesses in suppliers or partners | Supply chain breaches, reputational damage |
These risks demonstrate that cyber security is not solely a technical issue but a strategic business concern that requires cross functional involvement.
Mitigation Strategies for Cyber Security Risks
Efficient cyber security risk reduction entails the choice and adoption of controls that cut off risk to reasonable proportions. The mitigation measures are normally divided into physical, administrative and technical controls. The technical controls comprise firewalls, intrusion detection systems, encryption, and multi factor authentication. These controls defend the systems against inappropriate access and restrict propagation of attacks.
Technical routines such as vulnerability scanning and patch management are also necessary to minimize exposure to the familiar threats. Policies, procedures and human factors are the subject of administrative measures. Security awareness training will prepare the staff to identify phishing attacks and implement safe behavior. Clarity of incident response plans makes organisations be able to respond quickly and effectively to cyber incidents. Strictest access control policies that are grounded on the principle of least privilege minimize the chances of insider abuse.
Physical controls are also still applicable when it comes to the safety of hardware and critical infrastructure. Physical tampering and unauthorised access cannot occur because of secure server rooms, surveillance systems and controlled access points that would otherwise compromise the digital security measures.
Mitigation strategies for cyber security risks are essential to protect organisational data and systems. Effective mitigation strategies include regular software updates, employee training, network monitoring, and access control. Implementing these mitigation strategies reduces vulnerabilities, prevents breaches, and ensures business continuity. Continuous evaluation of mitigation strategies strengthens overall cyber resilience.
Read more:
https://www.balbix.com/insights/what-is-cyber-risk-mitigation
The Continuous Monitoring and Governance
Cyber security risk management is a continuous process and not a single instance. The use of continuous monitoring enables businesses to identify the emergence of the threats and evaluate the efficacy of the current controls. The security information and event management systems assist in real time visibility through networks and applications.
The role of governance structures is to ensure that cyber security is aligned with organisational goals. The involvement of senior management security would make sure that the cyber security risk is incorporated in the enterprise risk management processes. Open responsibility, frequent auditing and performance monitoring promote long term improvement and adherence to regulations.

Business Strategy Integration
A strong cyber security plan helps in business continuity and competitive edge. When organisations align their risk assessment and mitigation with their strategic priorities, they are able to protect the critical capabilities and also allow innovation. As an example, the secure cloud adoption and data analytics initiatives require strong foundations on cyber security.
Risk based analysis ought to be used to make investment decisions as opposed to generic compliance requirements. The strategy would provide the efficiency in resource distribution and organisational resiliency under dynamic threat conditions.
Conclusion
Businesses functioning in a more digital and connected environment need cyber security analysis and mitigation strategies. Cyber threats and operational stability can be improved by assessing the systematic risks, adopting the established frameworks, and applying the layered controls, which will allow organisations to avoid exposure to cyber threats.
Constant control, management and strategic alignment also safeguard that cyber security advances business long term goals. Risk management is an essential factor in organisational success as cyber menace keeps changing.
Frequently Asked Questions
Cyber security risk assessment is a structured process through which organisations identify digital assets, analyse potential threats and vulnerabilities, and evaluate the likelihood and impact of cyber incidents in order to prioritise security controls and investments.
Cyber security risk management is important because it protects sensitive data, ensures operational continuity, supports regulatory compliance, and reduces financial and reputational losses resulting from cyber attacks and system failures.
Commonly used frameworks include ISO 27001, the NIST Cybersecurity Framework, and COBIT. These frameworks provide systematic guidance for identifying, assessing, and mitigating cyber security risks across organisational processes.
The most common threats include phishing attacks, ransomware, insider threats, unpatched software vulnerabilities, and third party or supply chain security risks, all of which can significantly disrupt business operations.
Businesses can improve mitigation strategies by implementing layered technical controls, strengthening security policies and employee training, conducting regular audits and monitoring, and aligning cyber security governance with overall business strategy.

